Three approaches. One clear winner.
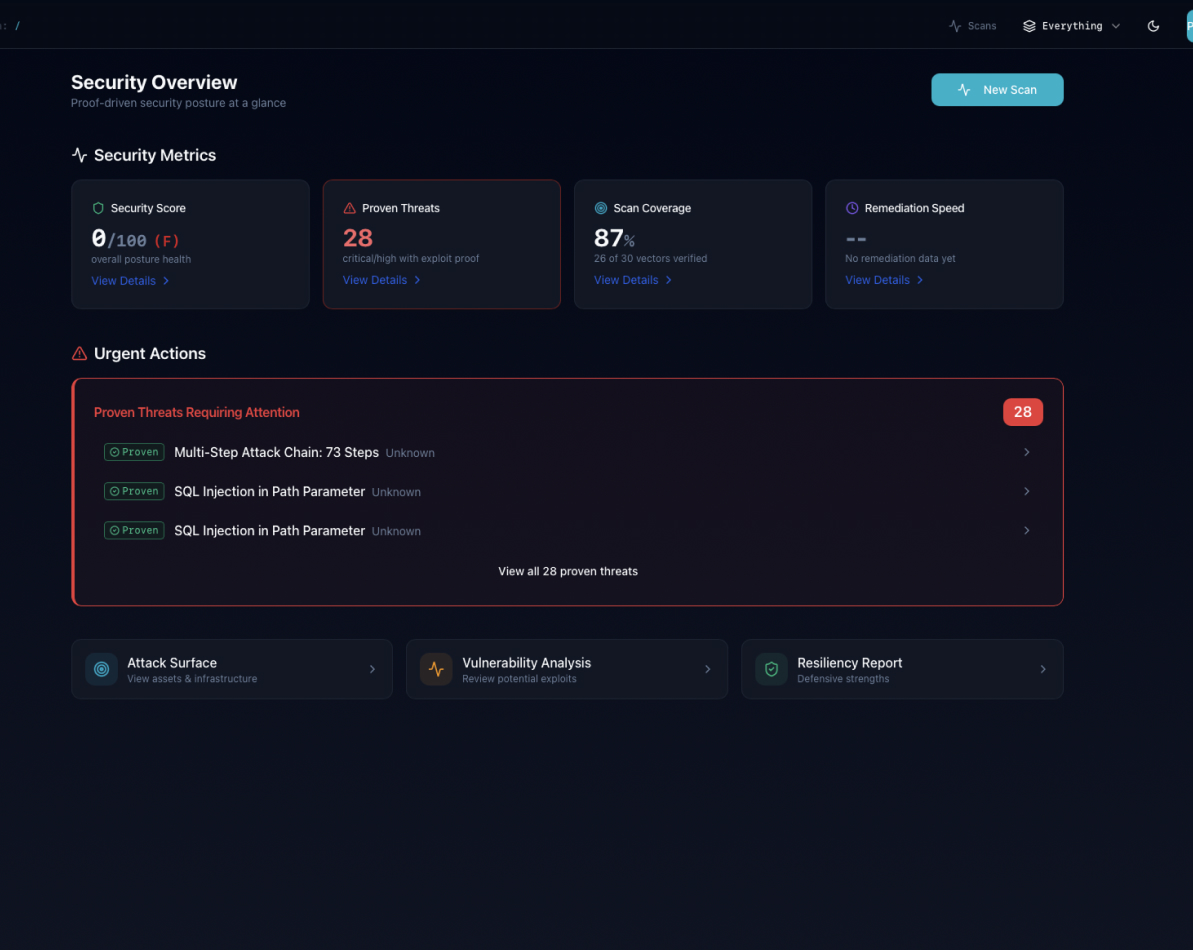
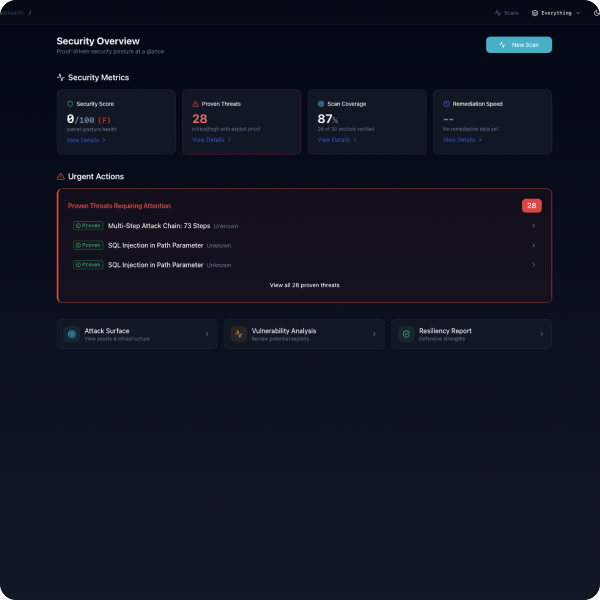
Gartner defines three distinct categories of security testing. Legacy scanners find vulnerabilities. Human-hybrid PTaaS proves some of them. Only Adversarial Exposure Validation continuously proves which ones are actually exploitable - without a human pentester.

EdgeAgent — The Field Operator
Deployed to interact with your targets. EdgeAgent performs reconnaissance, executes attack vectors, and captures evidence. It reports everything back to EdgeMind in real-time.
EdgeMind — The Intelligence Layer
The coordination layer that analyzes results, tracks what's been tested, and decides what to try next. EdgeMind maintains context across the entire engagement - remembering what worked, what didn't, and what to chain together.
Our Reasoning Model
A custom AI model built specifically for offensive security. Unlike general-purpose AI, our model generates attack vectors, reasons about application logic, and adapts payloads based on how your defenses respond.

Three stages that prove what actually matters

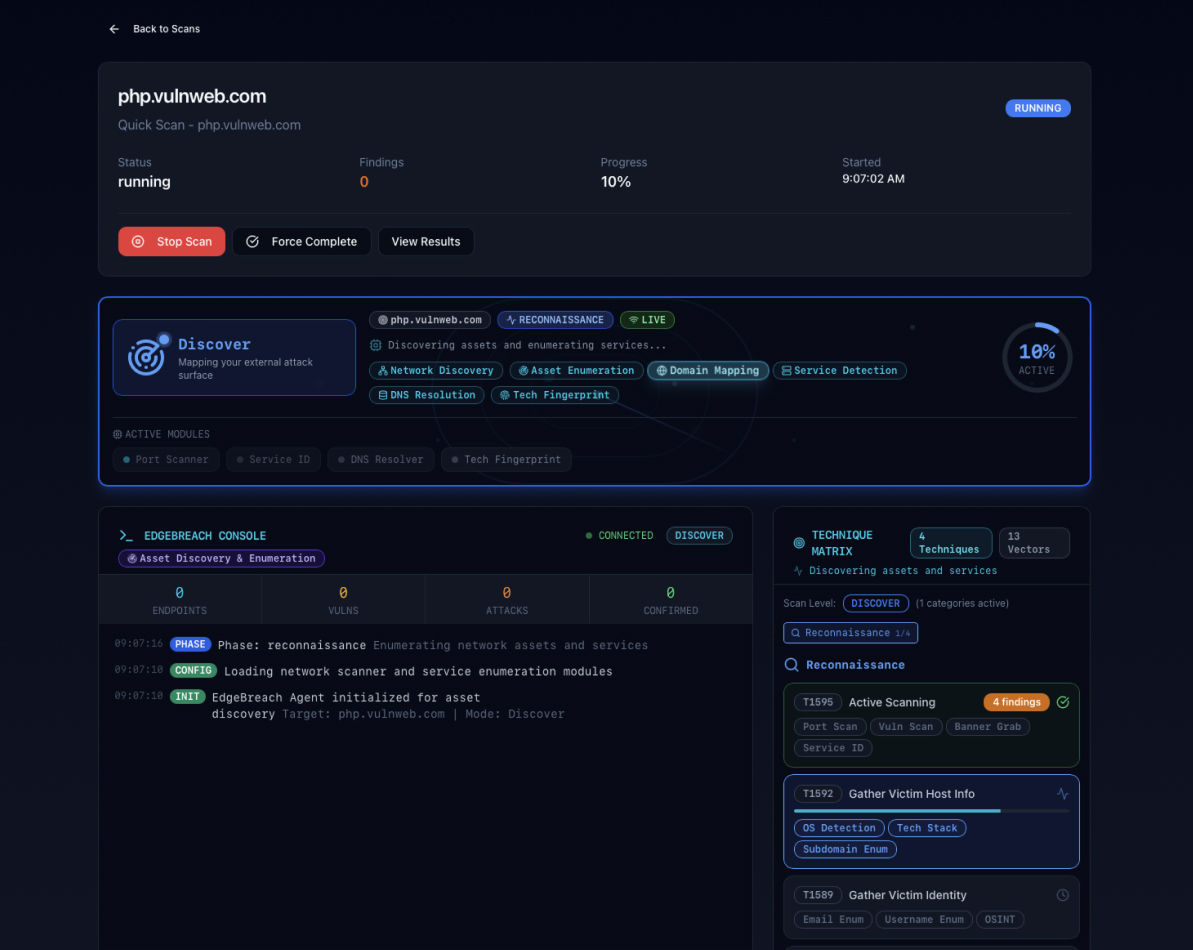
Map your attack surface before attackers do
EdgeBreach scans your entire infrastructure continuously, identifying every exposed service, port, and potential entry point. Real-time updates mean you see changes the moment they happen.
What happens:
- Port scanning and service detection
- Technology fingerprinting (frameworks, versions, configurations)
- API endpoint discovery
- DNS enumeration and subdomain mapping
- Cloud asset identification
Our fingerprinting uses multi-signal correlation - not just banner grabbing. We combine HTTP headers, error messages, cookies, and path patterns to build accurate technology profiles.

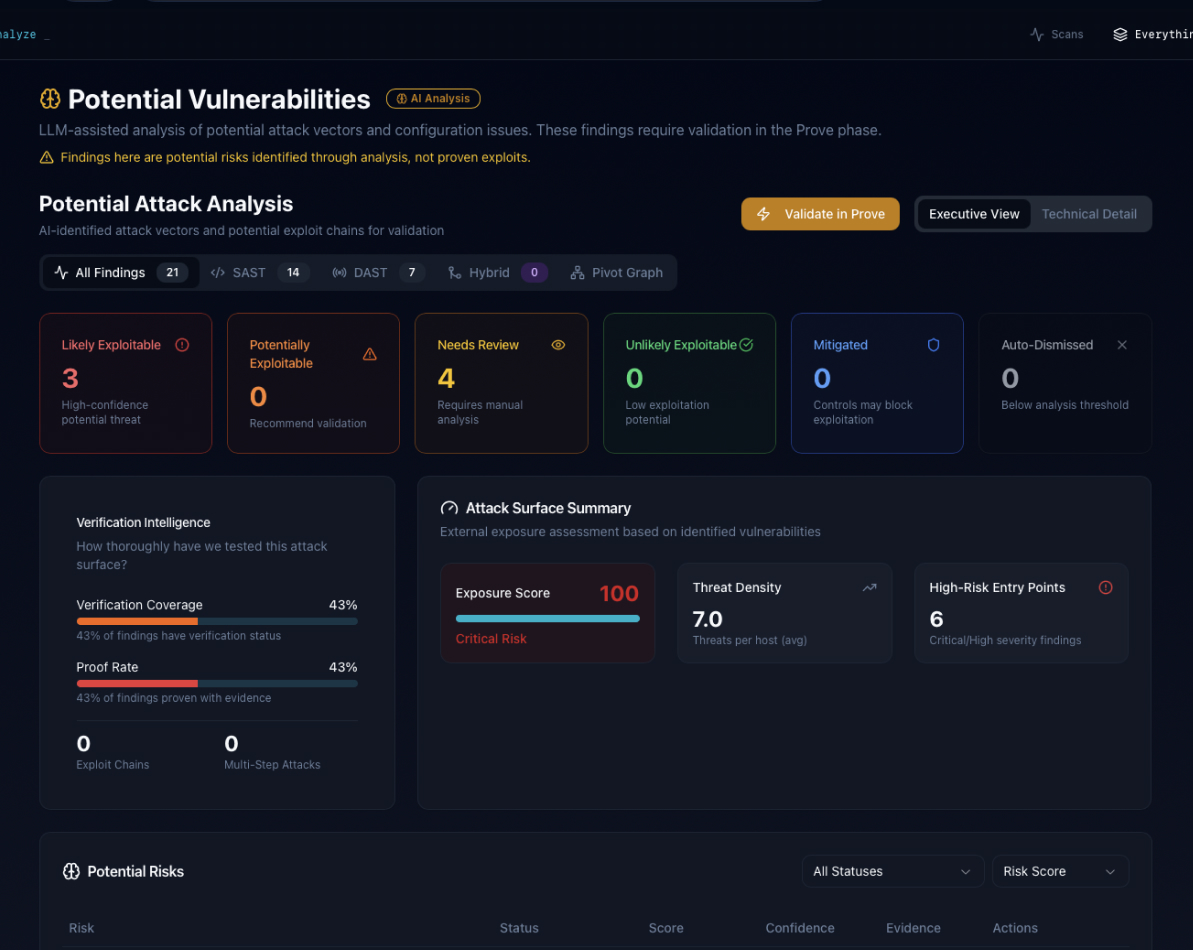
AI reasoning that learns your defenses
EdgeCore analyzes your environment and generates attack vectors specifically designed for YOUR technology stack, YOUR configurations, and YOUR defenses. Each test is unique.
What happens:
- Custom attack vector generation based on discovered technologies
- Business logic analysis (not just pattern matching)
- WAF detection and bypass selection
- Attack chain hypothesis formation
- Real-time adaptation based on responses
Traditional scanners ask: "Is this version in the CVE database?" EdgeBreach asks: "Given this Express API behind nginx with JWT auth, what attack chains should we explore?

Exploitation that shows what actually matters
EdgeBreach doesn't just report theoretical vulnerabilities. We chain findings into real attack paths, execute them, and capture evidence proving exactly what an attacker could do.
What happens:
- Vulnerability exploitation with evidence capture
- Attack chain execution (LOW + MEDIUM = CRITICAL)
- Screenshot and HTTP request/response capture
- Data extraction proof (with sensitivity handling)
- Remediation validation on demand
Every finding includes the proof. Not "possible SQL injection"—"SQL injection exploited, here's the extracted data, here's how to fix it."
What makes EdgeBreach different?
AEV is Simulation AND Exploitation
Most tools in this space either simulate attacks (Breach & Attack Simulation) or run automated scans, but rarely both in a single platform. Gartner explicitly calls this gap out. EdgeBreach discovers, chains, and exploits with evidence - unifying what competing tools sell separately.
AI-Native, Not AI-Wrapped
We didn't bolt AI onto a legacy scanner. EdgeBreach was built from the ground up for security testing - generating custom attack vectors, not parsing tool output.
Attack Chain Discovery
Real breaches aren't single vulnerabilities. They're chains. EdgeBreach automatically discovers how low-severity findings combine into critical exploits.
WAF Bypass Library
When a WAF blocks an attack, we don't stop. EdgeBreach tries 50+ bypass techniques to find what actually gets through -because attackers don't stop either.
Instant Remediation Validation
Fixed an issue? Click "Validate" and know immediately if it worked. No scheduling rescans. No waiting weeks. No hoping.
Evidence, Not Theories
Every proven finding includes screenshots, HTTP captures, and extracted data. Evidence your security team can act on and your auditors will accept.
Continuous, Not Annual
Stop relying on point-in-time annual pentests. EdgeBreach runs continuously, catching new vulnerabilities the moment they appear.
Map every endpoint before attackers find them
EdgeBreach scans your entire infrastructure continuously, identifying every exposed service, port, and potential entry point. Real-time scope updates mean you see changes the moment they happen.
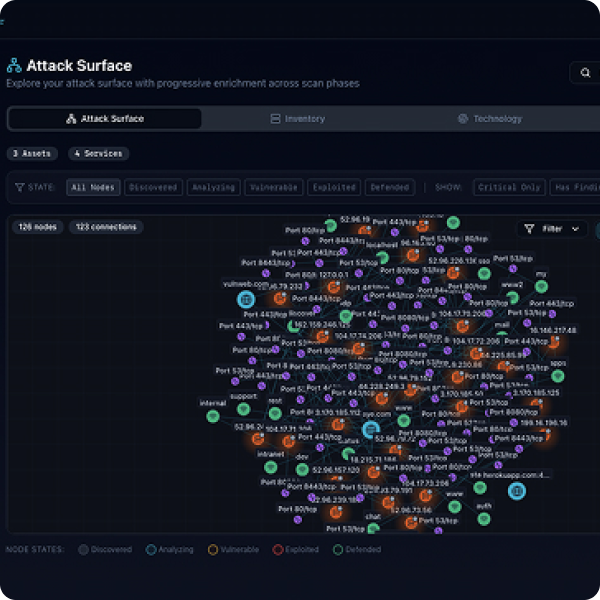
AI reasoning that learns your defenses
Our platform generates new attack vectors and payloads specifically designed for your environment, adapting in real-time as your security posture changes. Each test is unique, never running the same attack twice.
Exploitation that shows what actually matters
EdgeBreach chains vulnerabilities into real attack paths, demonstrating exactly which weaknesses can be exploited. You get evidence, not theories.
Questions
Security teams ask hard questions. Here are honest answers.
EdgeCore is a custom AI model trained specifically for offensive security. Unlike general-purpose AI that refuses to generate exploit code, EdgeCore was built to speak the language of attackers fluently. It generates real attack payloads, not generic suggestions.
We don't stop. EdgeBreach understands 50+ WAF bypass techniques just like the same methods real attackers use. We try encoding bypasses, chunked transfer attacks, and protocol-level evasion until we find what gets through. You'll know if your WAF actually protects you.
EdgeMind maintains context across the entire scan. When we find a user enumeration issue (low severity) and an IDOR on an API endpoint (medium severity), we don't just report them separately. We chain them: enumerate users → access each user's data = critical data breach. That's how real attackers think.
No. If you use white-box testing, your source code is processed in memory only. It's never written to disk and never stored. Code analysis happens in isolated, ephemeral environments that are destroyed immediately after the scan. We don't use your source code to train our models.
When you fix a vulnerability, click "Validate Remediation" in the dashboard. EdgeBreach immediately re-tests that specific finding and confirms whether the fix worked. No scheduling, no waiting, no extra cost. You know instantly if the issue is resolved.
Every proven vulnerability includes:
- Full HTTP request and response
- Screenshots showing the exploit
- Extracted data (if applicable)
- SHA256 hashes for integrity verification
- Step-by-step reproduction instructions
- Specific remediation guidance
EdgeBreach includes intelligent throttling and circuit breakers. We detect rate limiting, adjust our testing speed, and pivot to other attack vectors. If we see signs of system stress, we back off automatically. You can also configure scan intensity and timing windows.
Yes. EdgeBreach handles REST APIs, GraphQL endpoints, and complex single-page applications (SPAs). We understand modern authentication (JWT, OAuth), discover API endpoints automatically, and test for API-specific vulnerabilities like BOLA, broken function-level authorization, and mass assignment.
EdgeBreach uses anonymized attack patterns - successful techniques, bypass methods, and vulnerability signatures - to continuously improve EdgeCore. Your specific data (targets, source code, credentials) is never used for training. Only generalized patterns that can't identify you or your systems.
Black-box: We test from the outside, like an external attacker. No source code access, just what's publicly exposed.
White-box: You provide source code access (processed in memory only, never stored). This lets EdgeBreach find business logic flaws, hardcoded secrets, and vulnerabilities that aren't visible from the outside. White-box findings feed directly into attack vectors so we don't just report "potential issue," we prove it works.
When you fix a vulnerability, click "Validate Remediation" in the dashboard. EdgeBreach immediately re-tests that specific finding and confirms whether the fix worked. No scheduling, no waiting, no extra cost. You know instantly if the issue is resolved.
See how EdgeBreach finds what scanners miss
Get a personalized walkthrough showing how EdgeBreach would test your environment - and what it might find.