95% of security alerts are worthless
We prove the 5% that actually matter
EdgeBreach proves which vulnerabilities attackers can actually exploit. Continuous. Automated. Evidence-based.
How EdgeBreach finds what matters
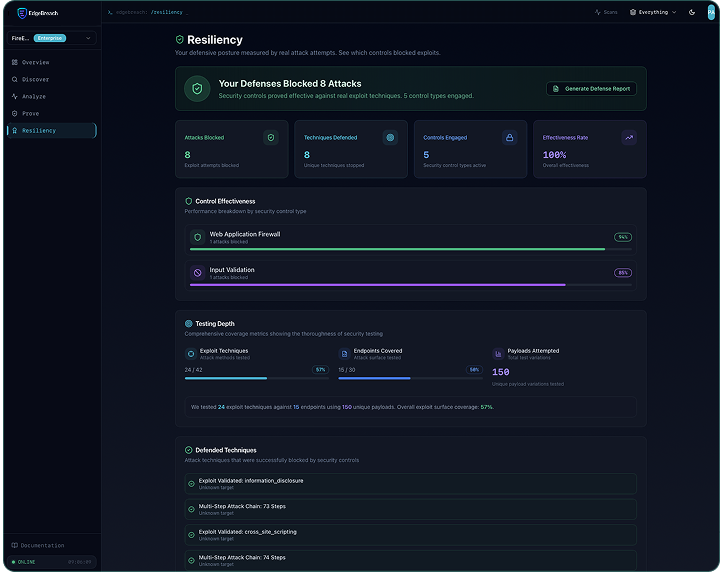
We map your attack surface, identify real vulnerabilities, and prove which ones can be exploited - delivering the Validation phase your CTEM program is missing.

Discover your attack surface
We map every exposed asset and entry point across your infrastructure.

Analyze for real vulnerabilities
AI identifies weaknesses and generates new attack vectors tailored to your environment.

Prove exploitability with evidence
This is the CTEM Validation phase. We validate each finding by actually exploiting it, showing you proof instead of theory.
AI native from the ground up
EdgeBreach isn't a scanner with AI bolted on. It's built from the ground up as an AI-native platform that reasons like a pentester, adapts to your defenses in real-time, and chains vulnerabilities into attack paths.
What you actually need to know
EdgeBreach cuts through the noise by proving which vulnerabilities matter. You get exploitability evidence instead of theoretical findings that waste your time.

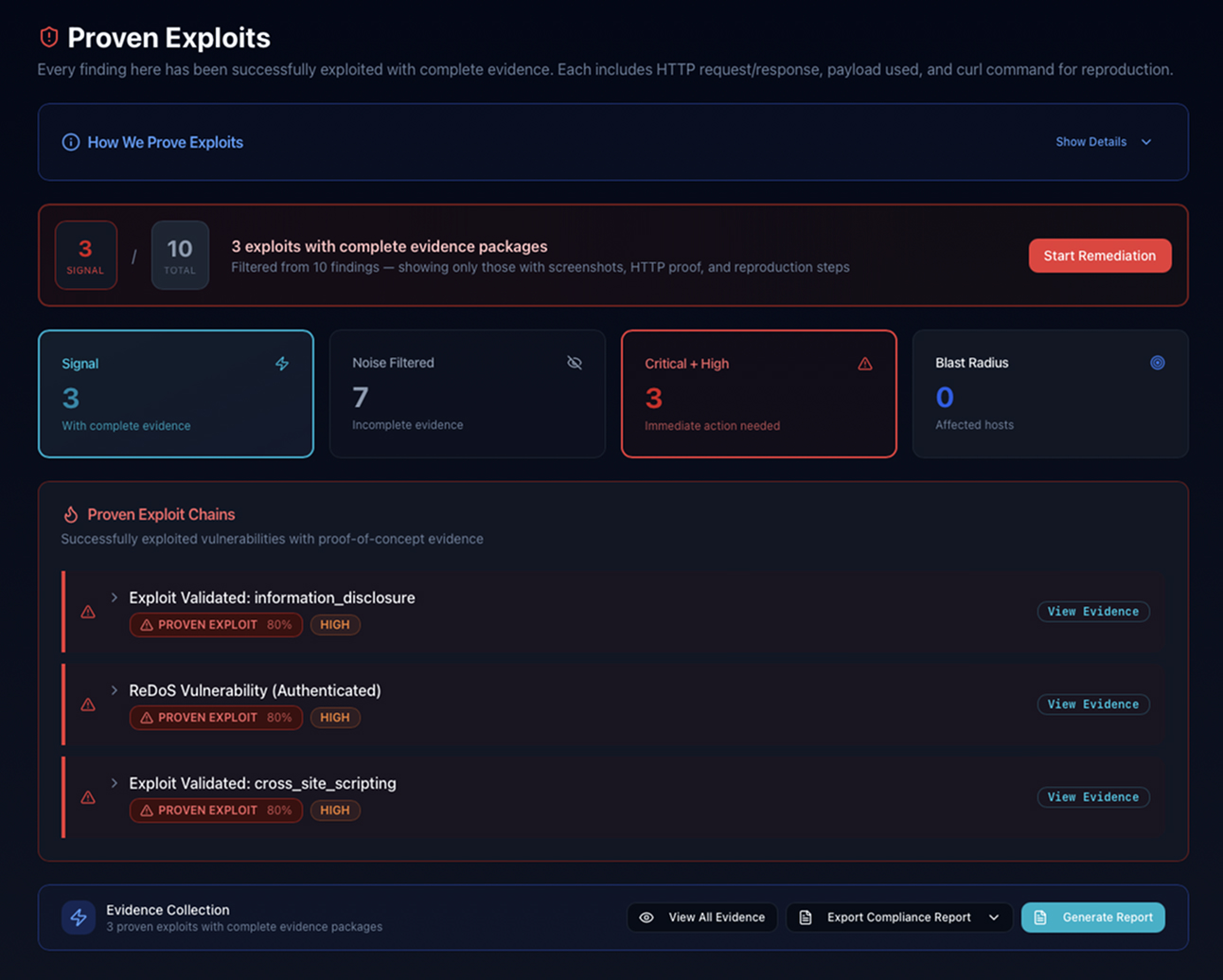
Proven exploits, not theories
We validate every finding by actually exploiting it.

Adapts as your defenses change
The platform learns your environment and generates new attack vectors in real-time.

Costs a fraction of annual pentests
Two to three years of continuous testing for what you'd spend on a single engagement.
The numbers behind continuous testing
Organizations waste time chasing false alarms while missing real threats. EdgeBreach cuts through the noise with proof, not theory. The math is simple: continuous testing costs less and finds more.
of scanner findings are false positives
of security professionals have missed a high-priority alert"
typical cost of annual pentest
From onboarding to evidence in less than 1 hour
EdgeBreach integrates with your infrastructure quickly and starts mapping your attack surface immediately. You see real results without the months of waiting.

Connect and configure
Link EdgeBreach to your environment and define your scope.

Continuous discovery and analysis
The platform maps assets, identifies vulnerabilities, and chains them into attack paths.

Receive exploitation proof
Each finding includes evidence showing exactly how it can be exploited.
FAQs
Common questions from security teams evaluating CTEM (Continuous Threat Exposure Management) and AEV (Adversarial Exposure Validation)
Can EdgeBreach replace our annual pentest?
For most organizations, yes. EdgeBreach delivers continuous Adversarial Exposure Validation (AEV), the Gartner-recognized standard for ongoing exploitability testing. For compliance-driven use cases (PCI-DSS, SOC 2), EdgeBreach-generated reports satisfy the independence and methodology requirements both frameworks mandate. For organizations that need auditor-signed reports as part of a specific certification process, we offer compliance-grade reports at Scale and Enterprise tiers.
How is this different from a vulnerability scanner?
Scanners flag theoretical vulnerabilities. EdgeBreach proves which ones are actually exploitable by executing real attacks and capturing evidence including screenshots, HTTP logs, extracted data. PCI-DSS explicitly distinguishes penetration testing (proven exploitability) from scanning (theoretical findings). Most scanners produce 80–95% false positives. EdgeBreach eliminates the noise.
What is Adversarial Exposure Validation (AEV)?
AEV is Gartner's defined category for technologies that deliver "consistent, continuous, and automated evidence of the feasibility of various attack scenarios, not only the existence but also the exploitability of exposures despite existing defensive controls." EdgeBreach is an AEV platform.
What is CTEM, and where does EdgeBreach fit?
Continuous Threat Exposure Management (CTEM) is Gartner's dominant strategic framework for security operations programs. It has five phases: Scoping → Discovery → Prioritization → Validation → Mobilization. Most organizations have tools for the first three phases. Almost none have a scalable, continuous solution for Validation, which is the step that separates real risk from theoretical noise. EdgeBreach is built for this phase.
Is EdgeBreach suitable for SMBs?
Absolutely. EdgeBreach gives you enterprise-grade security testing starting at $249/month, with no security expertise required to interpret results.
Still have questions?
If you still have questions, click below to reach our team and one of our specialists will setup a video call to discuss your questions.